Why Proof of Personhood Makes You a Validator — No Hardware Required
You Don't Need a Mining Rig. You Just Need to Be Human.
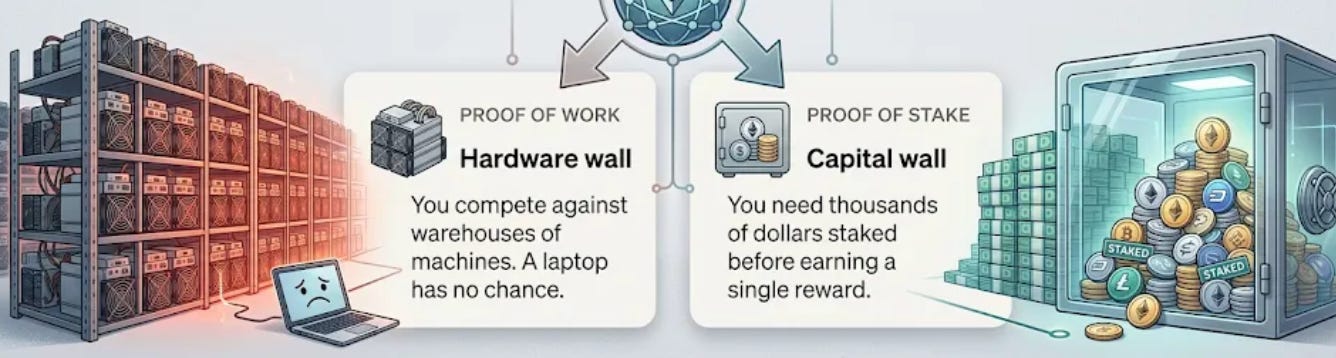
For more than a decade, participating in blockchain validation meant clearing one of two very high bars.
Both systems answered the same question — “Who has enough resources to participate?”
InterLink asks a different question entirely.
👤🔐 Proof of Personhood: validation by identity
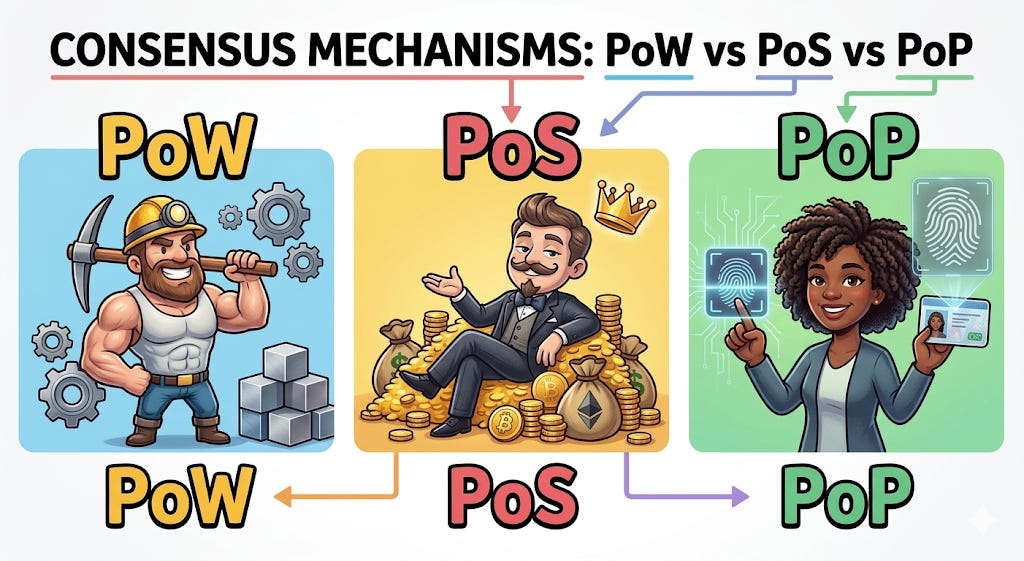
InterLink’s Proof of Personhood (PoP) introduces a third form of validation that sits alongside PoW and PoS.
Instead of hardware or capital, it requires one thing: proof that you are a unique, real human being.
The official InterLink Whitepaper states that PoP ties validation directly to real human identities through the InterLink ID. One verified identity equals one validation right. No more, no less.
This solves a structural problem that has plagued open networks since their beginning: Sybil attacks, where a single actor floods the system with fake accounts to manipulate consensus.
When identity is the credential, fake accounts cannot exist at scale. The network becomes resistant by design.
A student in Seoul, a freelancer in Lagos, a developer in Mumbai — each holds exactly the same validation weight. The playing field is level in a way no previous consensus model has achieved.
This is more than an engineering choice. In every prior model, validation power concentrated naturally over time — toward those who could afford more hardware, or accumulate more tokens.
PoP breaks that gravitational pull. Because identity cannot be purchased in bulk, the system has no mechanism for dominance by wealth.
The economics of validation are, for the first time, structurally flat.
🧬 What happens to your biometric data
The natural concern: if identity is the key, does InterLink store your face on a server somewhere?
The answer is no — and the architecture ensures it structurally, not just by policy.
When you verify, your biometric data is converted into a mathematical feature vector. The original image is deleted immediately.
That vector is then transformed into a cryptographic hash through Zero-Knowledge Proofs and Homomorphic Encryption — a one-way process that cannot be reversed.
Even InterLink itself cannot reconstruct your biometric data from what is stored.
Even if a node were compromised, an attacker would find only abstract numbers. Your identity proves your humanity to the network without ever leaving your control.
The significance of this extends beyond privacy compliance. At the entry level, participation does not require you to trust any single institution with sensitive data.
Trust is minimized by design — at the point of participation. The cryptographic design removes the need for that trust entirely.
KYC enters only at the point of asset migration. Not as a reversal of trustless design, but as a requirement of interfacing with regulated systems — no different from presenting identification at a bank counter.
You verify once, the proof persists, and the original data is gone. That is not a privacy policy — it is a privacy guarantee built into the protocol itself.
🎯 What this means for you, right now
PoW asked whether you had a powerful machine. PoS asked whether you had significant capital. PoP asks only whether you are real.
If you are, you already qualify.
The barrier is not resources — it is simply the decision to participate.
In systems where validation is tied to identity, positioning is not purchased — it is accumulated through participation over time.
The infrastructure is built. The identity layer is live. The question is when you join, not whether the system works.
The most democratic validator network ever built does not require a rig or a treasury. It requires a heartbeat. You already have one.
If you’d like to support my research, you may use my Interlink invitation code below. It also unlocks an instant mining boost ✚︎ Welcome Bonus for new users.
InterLink Referral Code: 905079415
Wallet Invitation Code : HSVZZPEJ (75% Commission Rebate)
❓ New to InterLink?
You don’t need capital. You just need five minutes.
📚 Done.T’s Related Insights
🔎 Search “Done.T Insight” on Google for real data & analysis.
Disclosure: This post contains referral links and reflects my personal research and experience. It is provided for informational purposes only and does not constitute financial advice.